Photo by krakenimages on Unsplash
AWS IAM Gotcha! Outsmarting the common pitfalls of securing your cloud
Recommended best practices
Table of contents
If you want to avoid headaches and potential unwanted use of your cloud resources, like for example, avoiding an unwanted bill for your EC2 instances (check my previous article if you'd like to know how EC2 pricing works), one of the most important skills you can have as a software developer is understanding how to properly manage access to your resources in the cloud. And when it comes to AWS, that means understanding the ins and outs of Identity and Access Management (IAM).
I get it but Miguel, please tell me... What is IAM?
AWS Identity and Access Management (IAM) is a web service that allows you to securely control access to your AWS resources. Think of it as the bouncer of your cloud infrastructure, granting or denying access to the right people and systems at the right time, all while keeping an eye out for any suspicious activity.
With IAM, you can create users, groups, roles, and policies to manage access to your resources, ensuring that only authorized entities can access and perform actions on them. In short, IAM is the key to keeping your cloud resources safe and secure.
First things first, let's talk about best practices...
One of the most important things to remember is that you should always create individual IAM users for anyone who needs access to your resources, rather than sharing AWS account credentials. This way, you can keep a better track of who is doing what, and you'll be able to revoke access more easily if someone leaves the company or doesn't need access anymore. AWS recommends creating a user even for yourself as the account administrator and assigning administrative privileges to it, rather than using your AWS root account.
Another best practice is to use groups to assign permissions to IAM users. This makes it much easier to manage permissions for multiple users at once. And if you ever need to change the permissions for a group of users, you can do it all in one place.
But what about when you need to grant access to other entities, like other AWS services or external identity providers? That's where IAM roles come in. These allow you to grant permissions to resources without having to create a new user or share credentials.
Of course, all of these users, groups, and roles need permission to do anything. That's where policies come in. You can use these to grant or deny permissions for AWS resources. And if you're feeling extra fancy, you can even write your own policies using the IAM policy language and JSON.
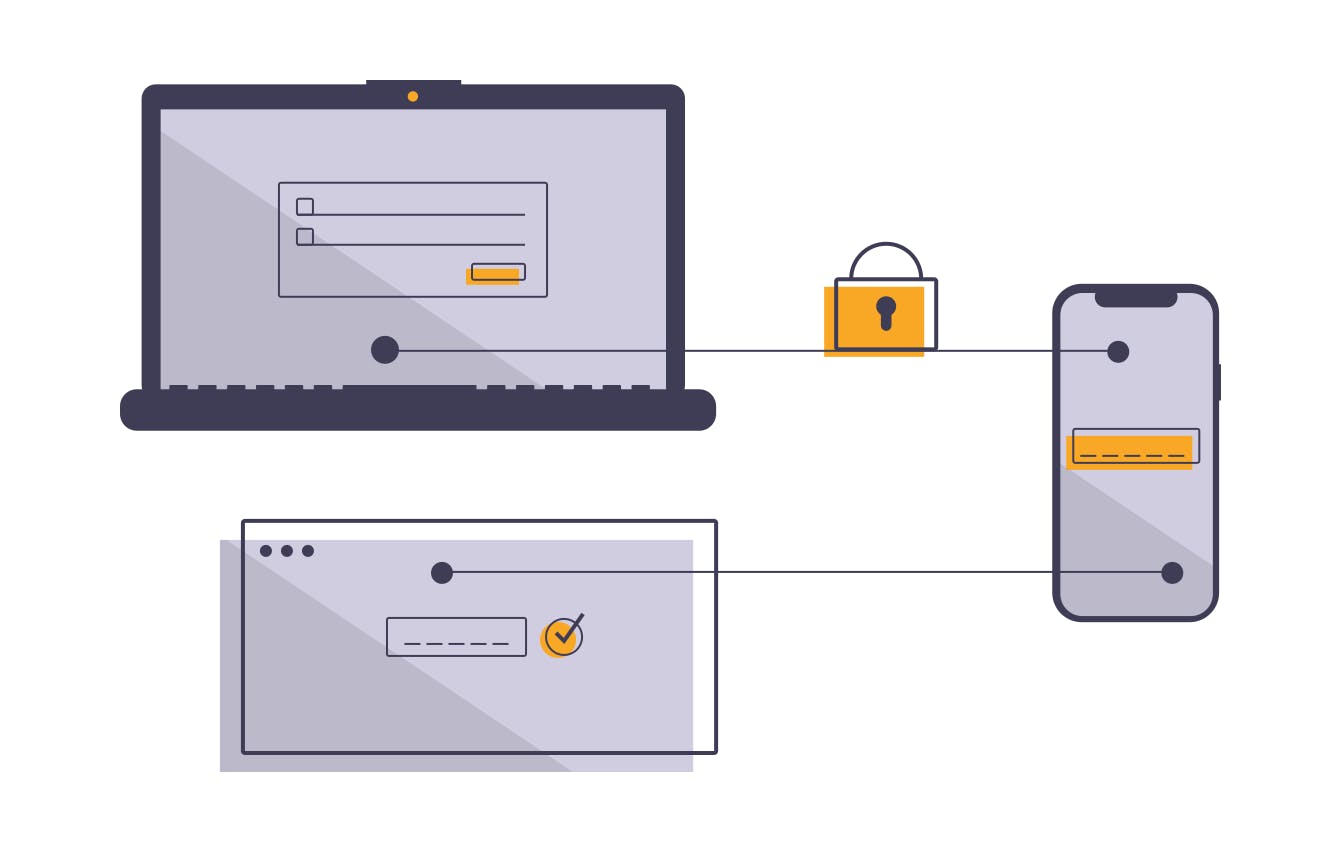
But all of these best practices are useless if someone can just guess your password. That's why you should always use multi-factor authentication (MFA) for added security. This way, even if someone does get a hold of your passwords, they won't be able to access your resources without that second form of authentication.
And speaking of security, it's important to rotate your security credentials regularly. This includes access keys, passwords and certificates.
Another important thing to keep in mind is the principle of least privilege. This means only giving users and processes the permissions they need to perform their tasks and nothing more. This helps to minimize the attack surface and prevent accidental data breaches.
And last but not least, monitor your IAM user activity regularly with AWS CloudTrail which is enabled by default. If you see anything unexpected, take action immediately. And if you want an extra layer of protection, use IAM Access Analyzer to identify and review resource access patterns and identify potential security issues.
Conclusion
All in all, AWS Identity and Access Management service is a powerful tool that can help you keep your cloud resources safe and secure. It may seem like a lot to keep track of, but with the right mindset and a little bit of practice, you'll be able to avoid common pitfalls when securing your cloud.